Concerned about the rising threat of cyberattacks affecting your business? You’re certainly not alone. Cyberattacks present a genuine risk to businesses like yours, potentially causing significant harm without a robust incident response plan in place. The good news is that an incident response plan can be a game-changer. In this article, we will delve into the common mistakes, myths, and misconceptions that can impede the development of a strong incident response plan. We’ll also provide practical solutions to help you navigate through cyber challenges more effectively. By steering clear of these pitfalls, you can fortify your response plan and enhance your business’s resilience against cyber threats.
Introduction: Crafting Your Incident Response Plan
The Importance of an Incident Response Plan
An effective incident response plan isn’t just a safety net; it’s a fundamental component of any modern business’s cybersecurity strategy. It serves as your playbook for swiftly and effectively dealing with potential cyberattacks. When a cyberattack strikes, every second counts. Having a clear, actionable plan in place ensures that your team knows exactly what to do, minimising damage and downtime. It also demonstrates to your customers that you take their data security seriously. Moreover, it can help mitigate legal and financial repercussions by ensuring compliance with data protection regulations. In essence, an incident response plan keeps you in control during what could otherwise be a chaotic and stressful situation, providing peace of mind for you and your stakeholders.
Recognising Cyberthreats
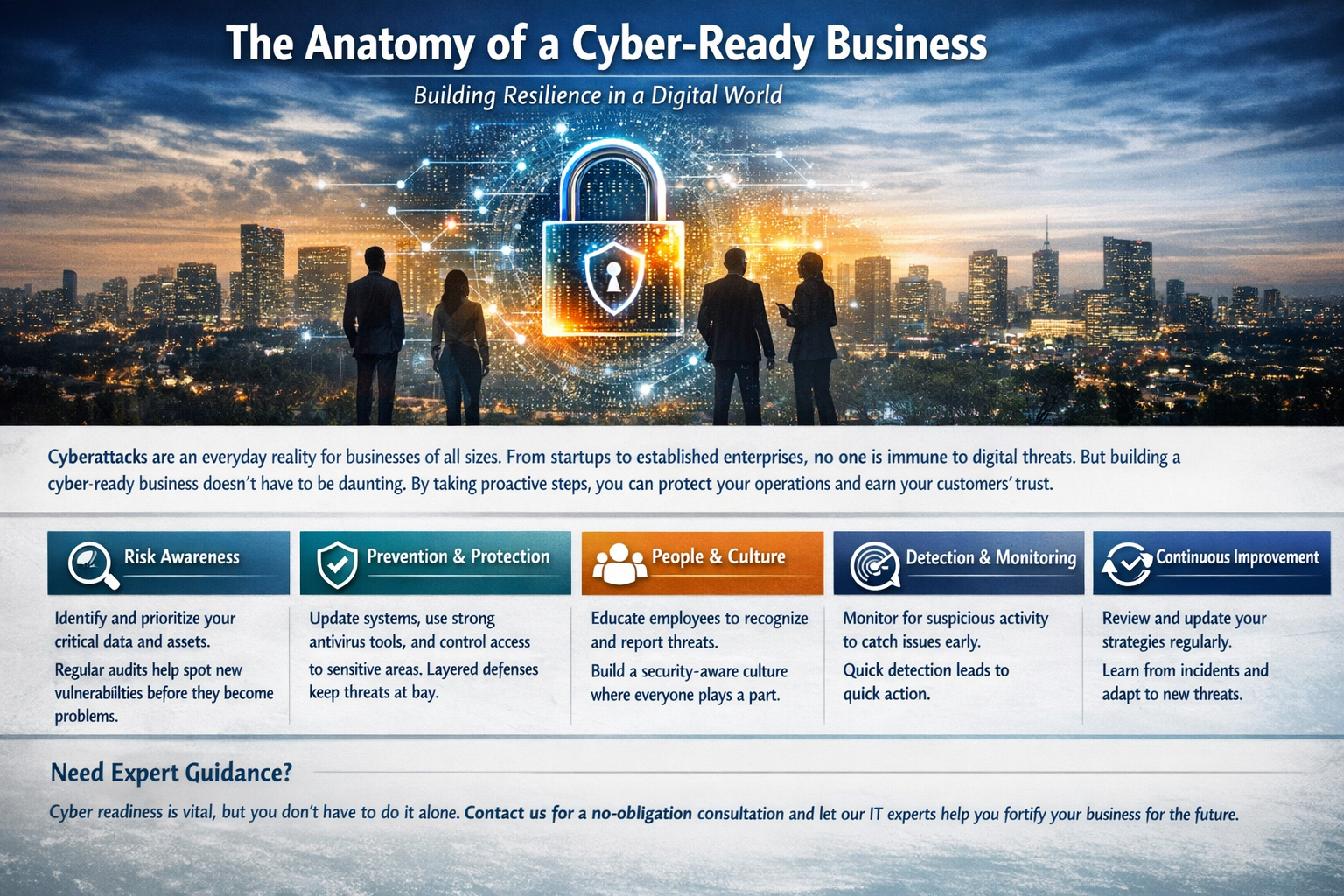
Understanding the myriad of cyberthreats is key to preparing your incident response plan. Cyberthreats can range from external attacks, like hacking and phishing scams, to internal threats, such as accidental data breaches or deliberate sabotage. Recognising that threats can emerge from anywhere and at any time is crucial. It’s not just the big companies that are targets; small to medium businesses are often seen as low-hanging fruit by cybercriminals due to typically having less stringent security measures. Keeping abreast of the latest types of attacks and common vulnerabilities within your industry will help you identify potential threats more quickly. This knowledge enables you to tailor your incident response plan to be more effective, ensuring that your business can withstand and quickly recover from any cyber incident.
Mistake 1: Ignoring Internal Threats
Understanding Internal Cyber-Incidents
When it comes to cybersecurity, many businesses focus on defending against external attackers. However, internal incidents, whether accidental or deliberate, can be just as damaging. Employees can unintentionally cause a breach by falling victim to phishing emails or by mishandling sensitive information. On the other hand, disgruntled staff might intentionally leak or sabotage data. It’s essential to recognise that these internal incidents are not just possible but are often the source of security issues. By prioritising measures like staff training, access controls, and regular audits, businesses can significantly reduce the risk of internal threats. Understanding the potential for such incidents and incorporating them into your incident response plan can make all the difference in safeguarding your company’s data and reputation.
Solutions and Preventive Measures
To combat internal cyber-incidents, it’s vital to implement a mix of technical and administrative controls. Start with comprehensive staff training on cybersecurity best practices and the importance of safeguarding company data. Encourage a culture of security awareness where employees feel responsible and empowered to report suspicious activities. Technically, enforce strict access controls and use the principle of least privilege, ensuring staff have access only to the information necessary for their job. Regularly update and patch systems to fix vulnerabilities that could be exploited by malicious software or disgruntled employees. Additionally, conduct routine security audits and have clear policies for both digital and physical security. By proactively addressing these areas, you can reduce the likelihood and impact of internal threats on your business.
Mistake 2: Overemphasising Technology
The Role of Technology in a Response Plan
While technology is a critical aspect of any incident response plan, it’s not a silver bullet. It’s easy to fall into the trap of believing that the latest cybersecurity tools will automatically protect your business from any threat. The truth is, technology should be one part of a multifaceted strategy. Cybersecurity technology can help detect breaches, protect data, and respond to incidents more quickly. However, without the right processes and a trained team in place, even the most advanced technology may fail to prevent or mitigate a cyberattack effectively. It’s essential to balance your investment in technology with the development of robust procedures and the continuous education of your team to ensure a comprehensive, proactive incident response capability.
Creating a Holistic Response Plan
To create a holistic incident response plan, you need to integrate technology with human insight. Start by defining clear roles and responsibilities for your team, ensuring everyone knows their part in the event of a cyberattack. Develop communication protocols to keep all stakeholders informed during an incident. Make sure your plan includes not only detection and containment but also recovery and post-incident analysis. Use tabletop exercises to simulate cyberattack scenarios and test your response procedures. This will help identify gaps in both your technology and processes. A holistic plan also considers the broader business impact, including public relations, legal implications, and business continuity strategies. By thinking beyond the technical solutions, you can develop a resilient plan that aligns with your business objectives and addresses the full spectrum of risks.
Mistake 3: Neglecting Updates to Your Response Plan
The Need for Regular Review and Update
A static incident response plan might as well be no plan at all. Cyberthreats are constantly evolving, and your defences must evolve too. Regularly reviewing and updating your plan is critical to ensure that it remains effective against the latest cyberattack strategies. This includes updating contact information for key personnel, revising procedures based on new insights, and integrating lessons learnt from recent incidents. Technology advancements should also prompt a review of your plan to incorporate new tools or methods that can improve your response. Furthermore, regulatory changes may require updates to maintain compliance. At least annually, or after any significant change to your business or technology infrastructure, take the time to reassess and refine your incident response plan to maintain its relevance and effectiveness.
Adapting Your Plan to the Evolving Threat Landscape
Cybersecurity isn’t a set-and-forget affair; it requires vigilance and adaptability. Adapting your incident response plan to the evolving threat landscape is crucial. This means staying informed about emerging threats and incorporating this intelligence into your plan. For instance, if ransomware is on the rise, ensure your plan includes specific strategies for containment and recovery. Make sure to factor in new technologies and platforms your business adopts, as these can introduce new vulnerabilities. Collaborate with cybersecurity experts to understand the implications of evolving threats and to receive recommendations for bolstering your defences. By making adaptation a regular part of your cybersecurity strategy, your business can stay one step ahead of cybercriminals, reducing the risk of a successful cyberattack and the potential damage it could cause.
Building Resilience: Partnering for Stronger Cybersecurity
The Benefits of an IT Partner in Incident Response
Partnering with a seasoned IT firm can significantly bolster your incident response capabilities. These partners bring specialised expertise and experience that your in-house team may lack, particularly in handling complex or sophisticated cyberthreats. They can provide insights into the latest cybersecurity trends and help you tailor your response plan accordingly. An IT partner can also offer additional resources during a crisis, such as a dedicated response team that can act quickly to mitigate the impact of a cyberattack. They often have advanced tools for monitoring and detection, which can be cost-prohibitive for many businesses to maintain on their own. Most importantly, an IT partner can work with you to develop a proactive cybersecurity posture, ensuring your business is not only ready to react to incidents but can also prevent many threats from materialising in the first place.
Choosing the Right Strategic Partner for Your Needs
Selecting the right IT partner is as crucial as having an incident response plan itself. Look for a partner with a track record of effectively managing cybersecurity issues in your industry. They should understand your business’s unique challenges and regulatory requirements. A good partner will work with you to enhance your existing cybersecurity measures, not just sell you generic solutions. Assess their responsiveness and ability to communicate complex issues in simple terms. It’s also valuable to check their own security practices; after all, they will be handling sensitive aspects of your business. Finally, ensure they offer scalability to grow with your business and adapt to changing threats. The right IT partner can transform your incident response plan from good to great, reinforcing your business’s defences against the ever-changing tide of cyber threats.